Recommended Blogs

The Business Case for DevOps Security: Implementation, Real Challenges, and Best Practices
Table of Content
- What is DevOps Security and Why it Matters for Your Business
- How DevOps Security Works: A Practical Implementation Guide
- The Real DevOps Security Challenges Holding Your Enterprises Back
- Best Practices in DevOps Security that Scale with Your Organization
- How TxMinds Empowers Businesses Build Secure DevOps at Scale
Here is a number that should make you as a business leader uncomfortable. 81% of companies are knowingly shipping vulnerable code into production. Not because the teams do not know better but because the pressure to release simply outweighs the time it takes to fix the problem.
That trade-off might feel manageable in the short term. One exposed credential, one misconfigured pipeline, one overlooked dependency is all it takes to hand an attacker the keys to your entire environment. And when that happens, the cost is not just technical. It is financial, operational, and reputational.
DevOps changed how fast businesses could build and ship. But speed without security built into the process is just a faster way to create risk. This blog breaks down what DevOps security means for your business, how to implement it properly, what keeps getting in the way, and what it takes to get it right for good.
Key Takeaways
- 81% of companies are knowingly shipping vulnerable code into production, showing how release pressure often outweighs security fixes.
- DevOps security works best when security is built into every stage of the SDLC, not treated as a final review before release.
- Practices like SAST, DAST, secrets management, least-privilege access, and continuous monitoring help reduce risk without slowing delivery.
- The biggest barriers are not just tools but organizational issues like speed-vs-security tension, cloud misconfiguration, cultural silos, and skills gaps.
What is DevOps Security and Why it Matters for Your Business
Most businesses understand DevOps as a way to ship software faster. Fewer understand what happens to their risk profile when they do. DevOps security, also called DevSecOps, is the practice of embedding security into every stage of the software development lifecycle rather than treating it as a final checkpoint. Development, operations, and security stop working in silos and start sharing responsibility for how software is built, tested, and delivered.
For a long time, security was considered at the end of the pipeline. Teams would build, test, and ship, then hand things over for a security review. By that point, fixing vulnerabilities was expensive, slow, and disruptive. Moving security earlier changes that equation entirely. Here is why it matters for your business specifically:
- Vulnerabilities caught in development cost a fraction of what they cost in production.
- Automated security checks reduce the burden on your team without slowing release cycles.
- Shared ownership across dev, ops, and security means fewer gaps and clearer accountability.
- Customers and regulators increasingly expect security to be built in, not bolted on.
- A secure pipeline is a faster pipeline because you stop recycling the same fixes sprint after sprint.
How DevOps Security Works: A Practical Implementation Guide
Implementing DevOps security is not a one-time task. It is a set of decisions a business makes about how teams build, test, and ship software, and then keep making as the environment grows. Once these decisions are embedded into the pipeline, they largely run themselves.
Here is how mature organizations put it into practice:
- Start with shift-left security: Move security checks as early in the development cycle as possible. When a vulnerability is caught while code is being written, fixing it takes minutes. When it surfaces in production, it can take weeks and cost significantly more in both time and trust.
- Embed automated testing inside your CI/CD pipeline: Static Application Security Testing (SAST) scans source code for flaws before it runs. Dynamic Application Security Testing (DAST) tests live application behavior in pre-production. Both should run automatically at every build, not on demand.
- Treat your infrastructure as code: Infrastructure templates, configuration files, and deployment scripts carry the same risk as application code. Scan them the same way and lock down access at every layer. Every human and machine credential in a DevOps environment is a potential attack vector. Enforce least privilege, eliminate hardcoded secrets, and rotate credentials on a defined schedule.
- Monitor continuously, not periodically: Security does not stop at deployment. Logging, alerting, and anomaly detection need to run across every layer of your stack around the clock. Issues that go undetected for days become significantly harder and costlier to contain.
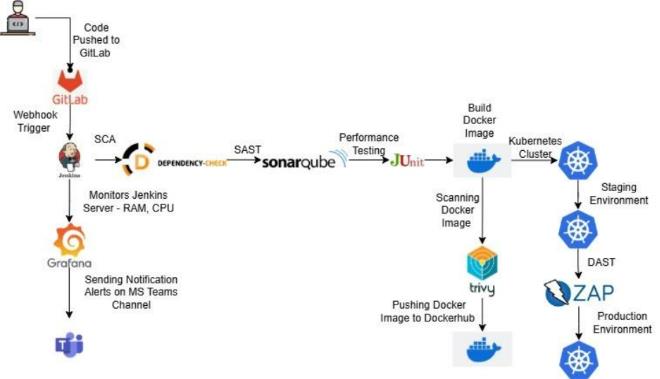
What this looks like in practice is often referred to as a DevSecOps pipeline, where security is not a separate stage but embedded directly into the CI/CD workflow. Each step, from code commit to production deployment, includes automated security checks and validation gates that ensure risks are identified and addressed early.
A DevSecOps workflow like this helps organizations turn security from a release blocker into a continuous assurance layer across development and deployment. The result is faster delivery, stronger governance, and fewer avoidable risks in production.
The Real DevOps Security Challenges Holding Your Enterprises Back
Majority enterprises struggle with DevOps security not because they lack the right tools but because the problem run deeper than technology. Here are some DevOps security challenges that limits a business growth:
Speed vs. Security
Every release cycle carries the same tension. Developers are measured on how fast they ship. Security teams are measured on how little goes wrong. Those two incentives pull in opposite directions, and without a shared framework, security almost always loses to the deadline.
Secrets Sprawl
Hardcoded API keys, passwords, and tokens sitting inside CI/CD scripts or source code repositories are one of the most exploited vulnerabilities in modern pipelines. The problem is not that teams do not know better. It is that without centralized secrets management, shortcuts become habits.
Cultural Silos
When development, operations, and security teams operate in isolation, nobody owns the full picture. Security gets treated as someone else’s problem until something breaks. Closing this gap requires more than a new tool. It requires a deliberate shift in how teams are structured and how work gets handed off.
Cloud Misconfiguration
A single misconfigured S3 bucket or overly permissive IAM role can expose an entire production environment. As cloud adoption accelerates, the margin for configuration error grows with it, especially across multi-cloud and hybrid setups where governance is inconsistent.
Toolchain Vulnerabilities
The very tools that power DevOps, including Jenkins, GitLab, Kubernetes, and Ansible, can become attack vectors if they are not patched, monitored, and hardened. An unsecured build server is an open door.
The Skills Gap
Developers are not security engineers and security teams are often not fluent in modern CI/CD tooling. That gap in expertise creates blind spots on both sides and makes it difficult to build a pipeline where security is everyone’s responsibility.
Best Practices in DevOps Security that Scale with Your Organization
Getting DevOps security right requires building the right habits early so they hold up as your business grows. Below are some best practices in DevOps security to ensure that it scales as your company grows:
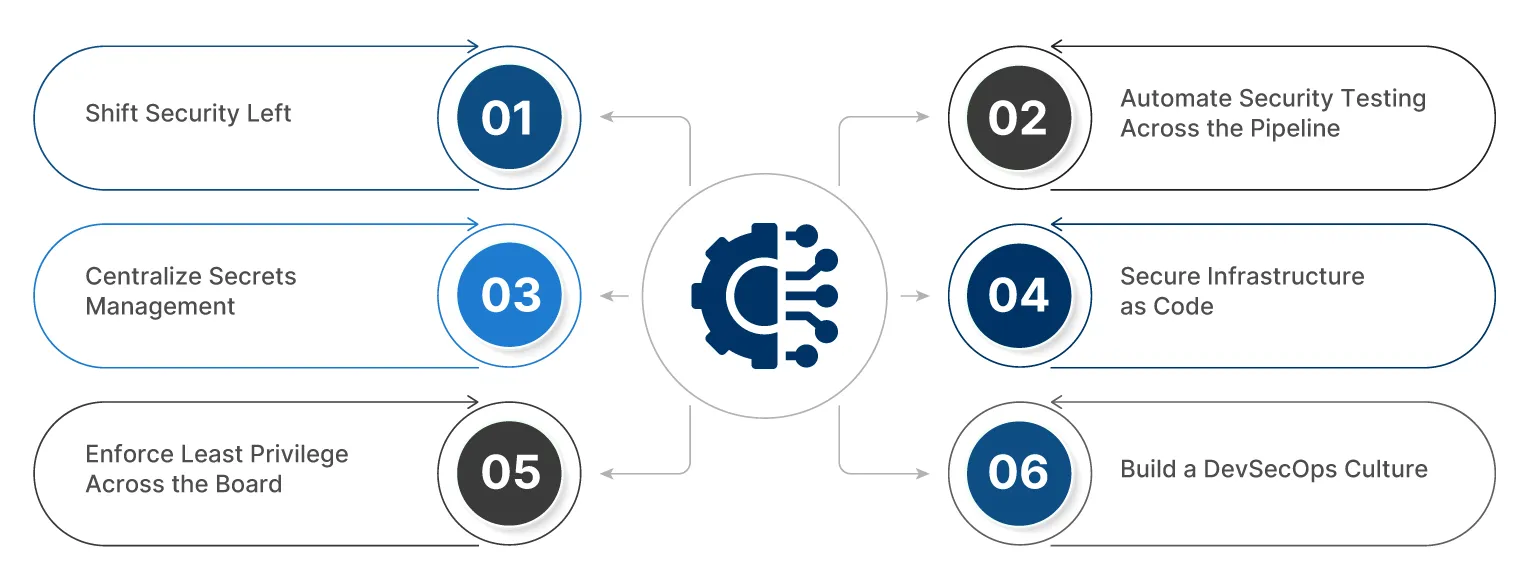
1. Shift Security Left
Integrate Static Application Security Testing (SAST) and Software Composition Analysis (SCA) directly into the development phase. When developers get security feedback inside their existing workflow, they fix issues without it ever becoming a formal process.
2. Automate Security Testing Across the Pipeline
Manual reviews do not scale. Embed Dynamic Application Security Testing (DAST), dependency scanning, and container image scanning into every CI/CD run. The pipeline catches what humans miss and do it consistently every single time.
3. Centralize Secrets Management
Stop storing credentials, API keys, and certificates in code repositories or environment variables. Use a dedicated secrets management platform so that rotation, access control, and auditing happen at the platform level, not through individual developer discipline.
4. Secure Infrastructure as Code
Every Terraform template, Helm chart, and Kubernetes manifest is a potential misconfiguration waiting to happen. Version control them, scan them, and enforce policy as code so that insecure configurations never make it to deployment.
5. Enforce Least Privilege Across the Board
Use Identity and Access Management (IAM) to ensure every human user and service account only accesses what it genuinely needs. Standing admin access is one of the most avoidable risks in any cloud environment.
6. Build a DevSecOps Culture
Tools enforce behavior but they do not create ownership. Run security champions programs, include security criteria in sprint definitions, and make post-incident reviews a learning exercise rather than a blame exercise. Culture is what makes the rest of this stick at scale.
How TxMinds Empowers Businesses Build Secure DevOps at Scale
Understanding what good DevOps security looks like and getting there are two completely different things. Most enterprises are aware of the gaps but unsure where to start or how to scale without disrupting what already works.
It is where TxMinds helps enterprises close that gap. Our DevSecOps implementation and automation services are built around the idea to keep security a natural part of how your pipeline runs and not a layer on top of it.
From embedding SAST and DAST testing inside CI/CD pipelines to automating infrastructure provisioning with Terraform and Ansible, TxMinds handles both the technical build, and the process change that makes it stick. Our continuous monitoring practice keeps visibility live across every environment, so teams are responding to real signals rather than discovering problems through incidents.
If your business is ready to stop treating security as a bottleneck and convert it to an advantage, we are the right partner to get you there. Speak with our DevSecOps experts and build a roadmap that works for your business goals.
FAQs
-
DevOps security (DevSecOps) integrates security across the SDLC by shifting security left, automating testing in CI/CD, securing infrastructure as code, enforcing access controls, and enabling continuous monitoring.
-
Key challenges include speed vs security conflicts, secrets sprawl, cloud misconfigurations, and skill gaps, which can be addressed through automation, centralized secrets management, policy enforcement, and team alignment.
-
Best practices for DevSecOps implementation include adopting shift-left security, automating SAST/DAST and dependency scanning, enforcing least privilege, securing infrastructure as code, and building a culture of shared security ownership.
-
To integrate security into DevOps pipelines, embed automated security checks like SAST, DAST, and container scanning into every CI/CD stage, ensuring vulnerabilities are detected and fixed early without slowing releases.
Discover more